Exercise 1: Hiding Information within a File
Installed SilentEye, using the defaults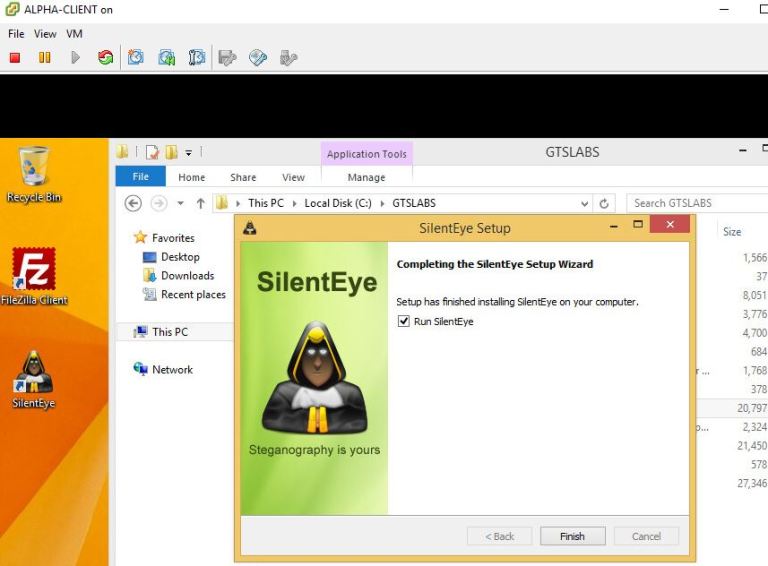
Inspected the properties of the image file ‘gtslearning.jpg’ and noted both the file-size, as well as dates and times of ‘created’, ‘modified’ and ‘accessed’.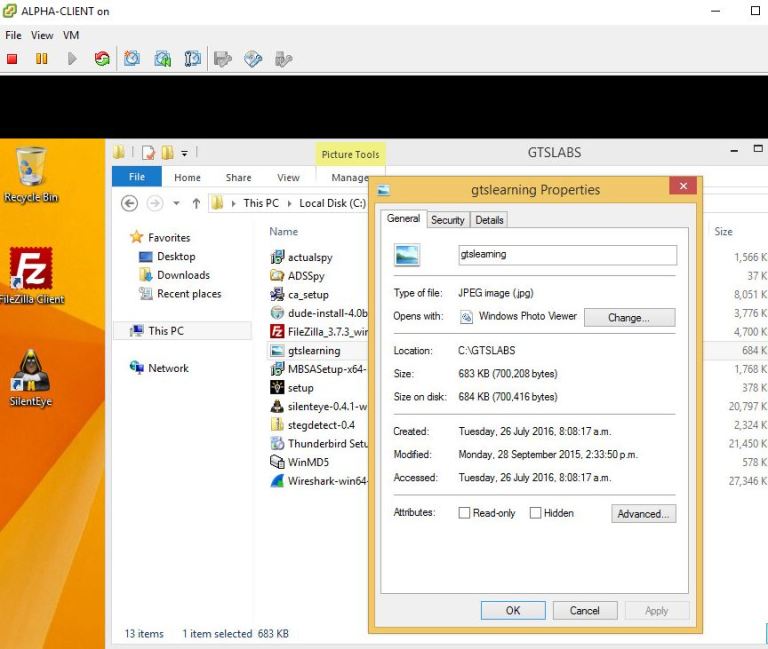
Opened WinMD5 dragged ‘gtslearning.jpg’ into the ‘select a file’ box and so created a checksum for the file. Also copied this ‘current’ checksum into the ‘original’ checksum box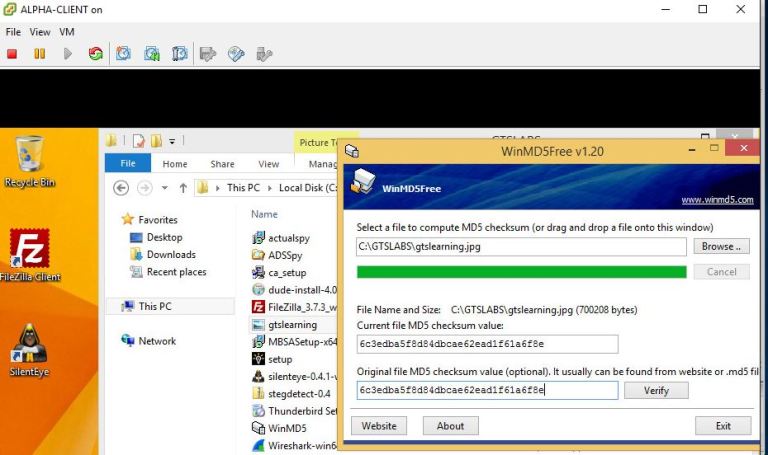
Selected the ‘gtslearning.jpg’ file in the ‘SilentEye’ window and clicked ‘Encode’. Typed ‘SilentEye’ in the message box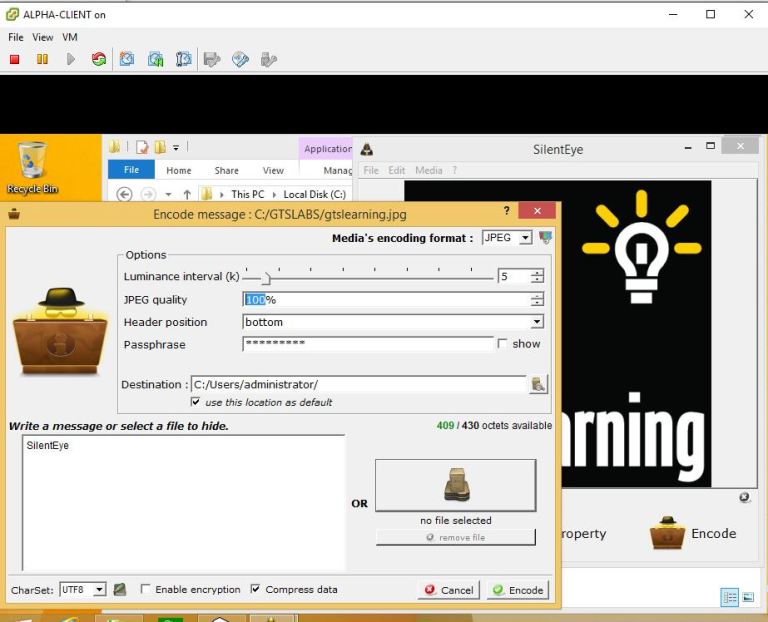 Set the ‘JPEG quality box’ to 100% and clicked ‘Encode’, then closed the ‘SilentEye’ window.
Set the ‘JPEG quality box’ to 100% and clicked ‘Encode’, then closed the ‘SilentEye’ window.
Typed ‘%homepath%’ in file explorer address bar to navigate to folder where ‘SilentEye’ output had been saved. Inspected the new file’s properties to find that the file that had just been created was significantly smaller (43.4 KB vs 683 KB)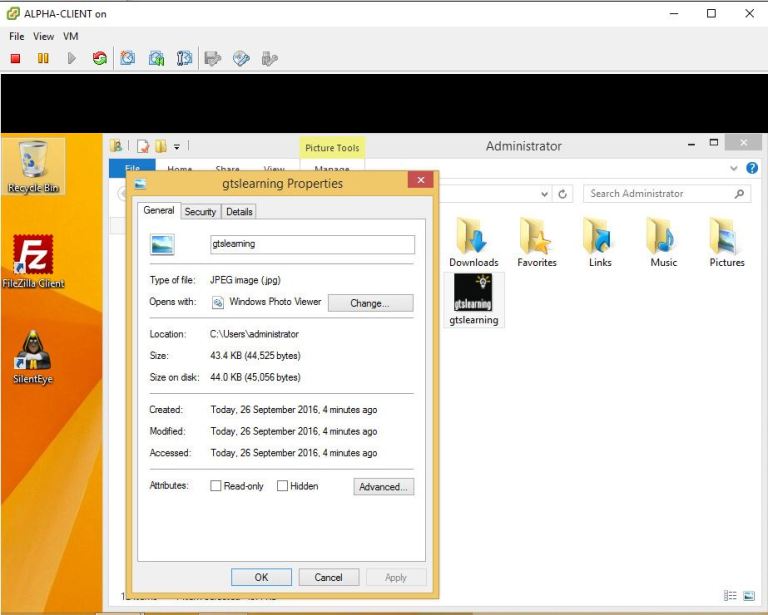
As expected the new file generated a completely different checksum, as seen below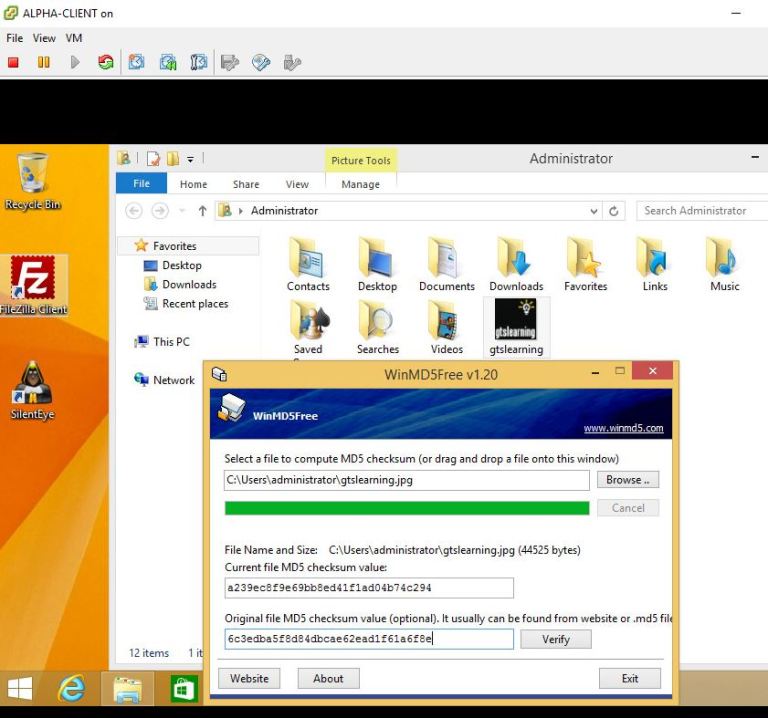
Exercise 2: Detecting Steganography
Opening previews of both files shows that the ‘new’ gtslearning.jpg has grey dots all over the black part of the picture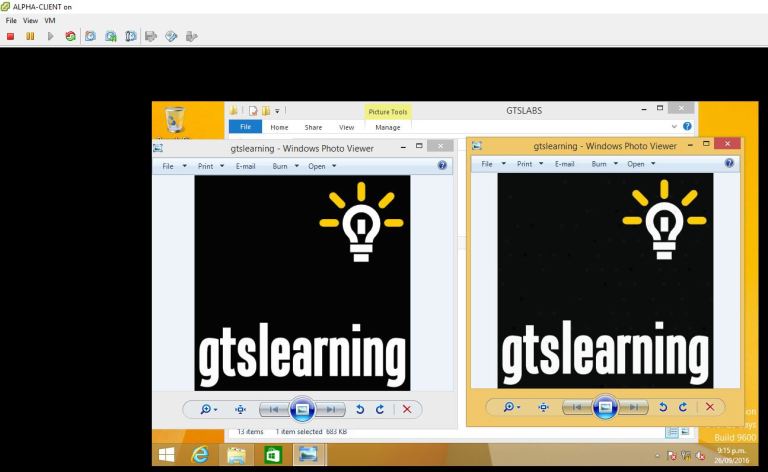
When running the ‘xsteg’ application and selecting the ‘new’ image file, ‘xsteg’ detects a hidden message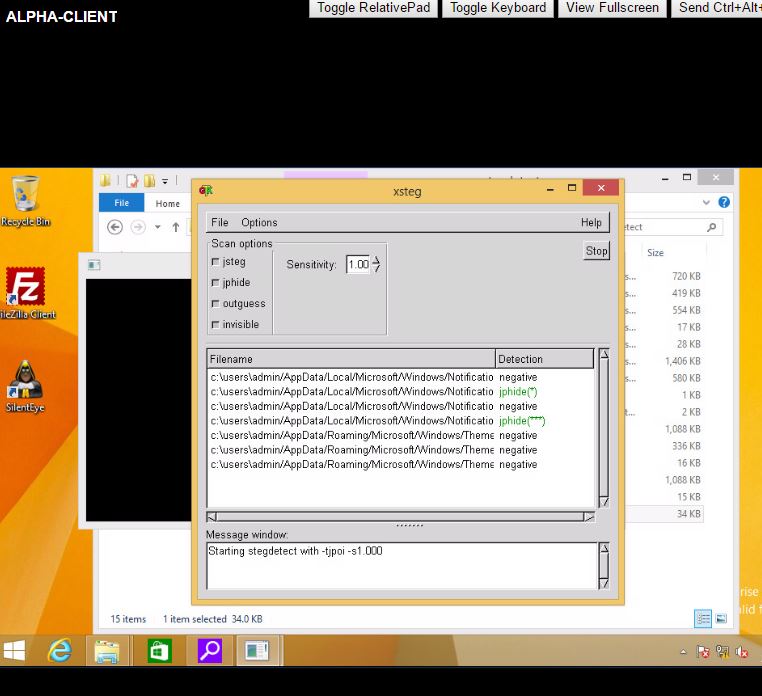
Exercise 3: Alternate Data Streams
Created a new Rich Text Document, according to instructions, calling it ‘MEMO’ adding ‘Alternate Data Streams’ as text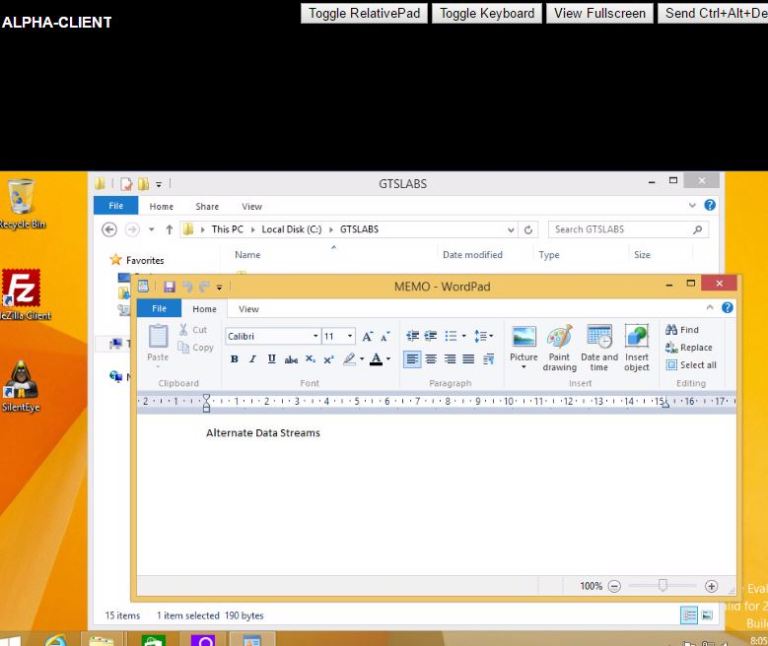
In properties noted the file-size (190 bytes) and date properties (2 min prior)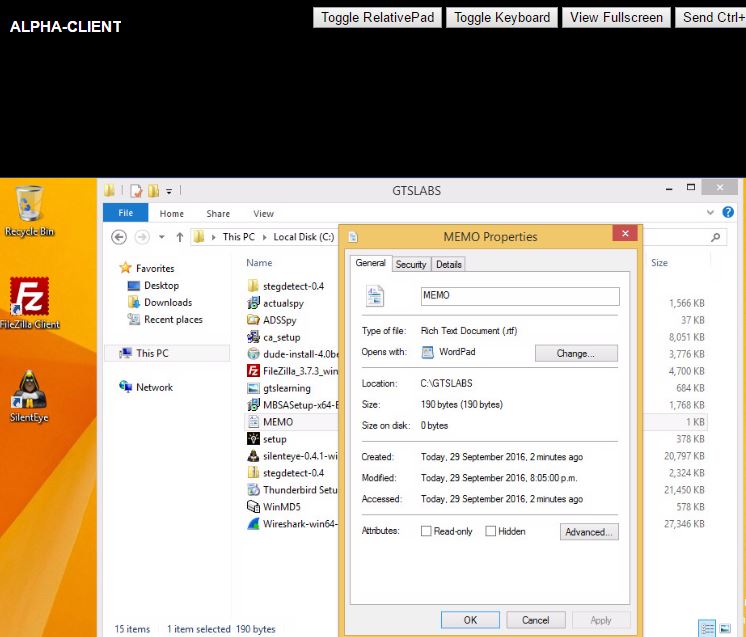
Dragged the ‘MEMO.rtf’ file into WinMD5 to create checksum, and copied ‘current’ checksum into ‘original’ checksum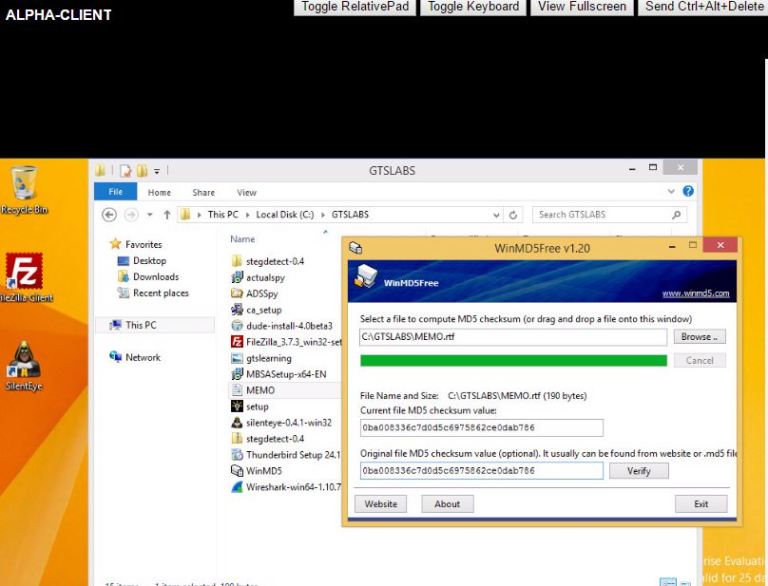
Opened command prompt and executed the commands given in the lab instructions, as seen below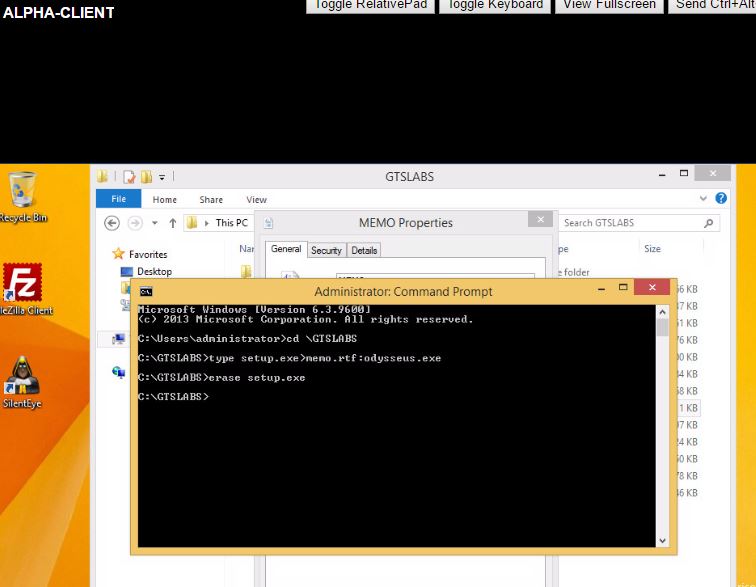
Inspecting the properties of the ‘MEMO’ file after executing the commands, shows that the file has been modified: file-size remained the same, but the ‘size on disk’ rocketed from 0 bytes to 380 KB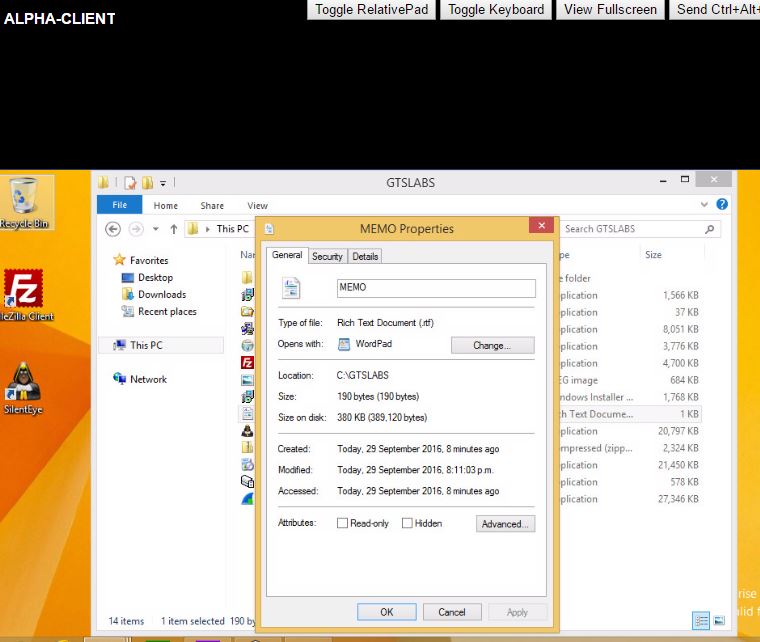
However, the checksum hasn’t changed, since the file-size itself hasn’t changed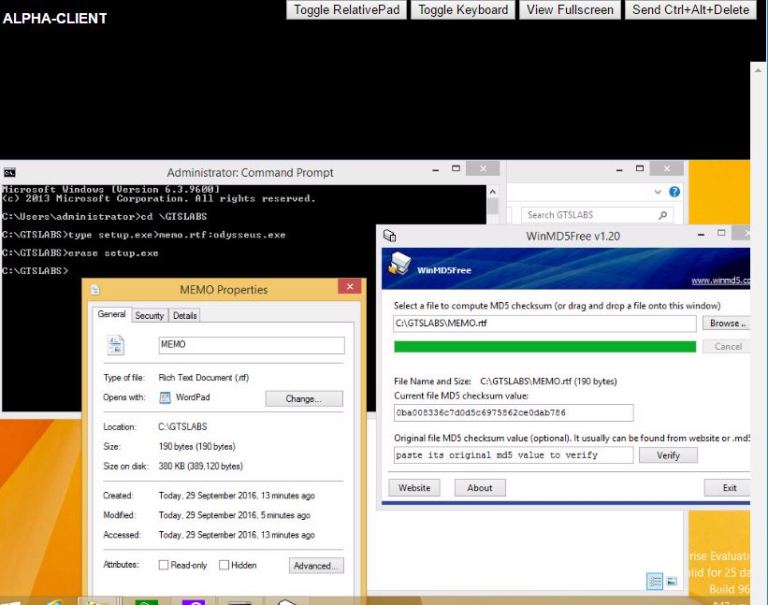
Move the file to Documents folder, double-clicked to open the file, but the ‘Odysseus.exe’ doesn’t run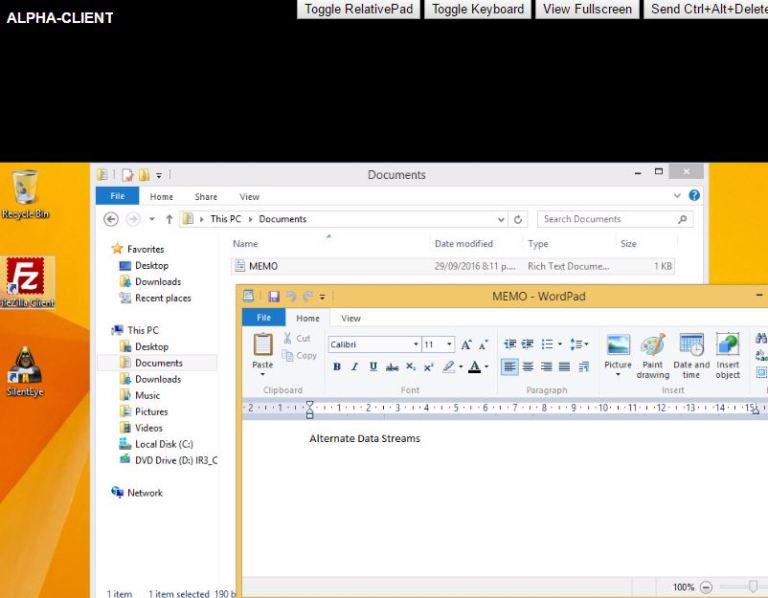
If however the below shown command prompt is run in the ‘Documents’ library, the ‘Odysseus’ setup wizard pops up and want to run the program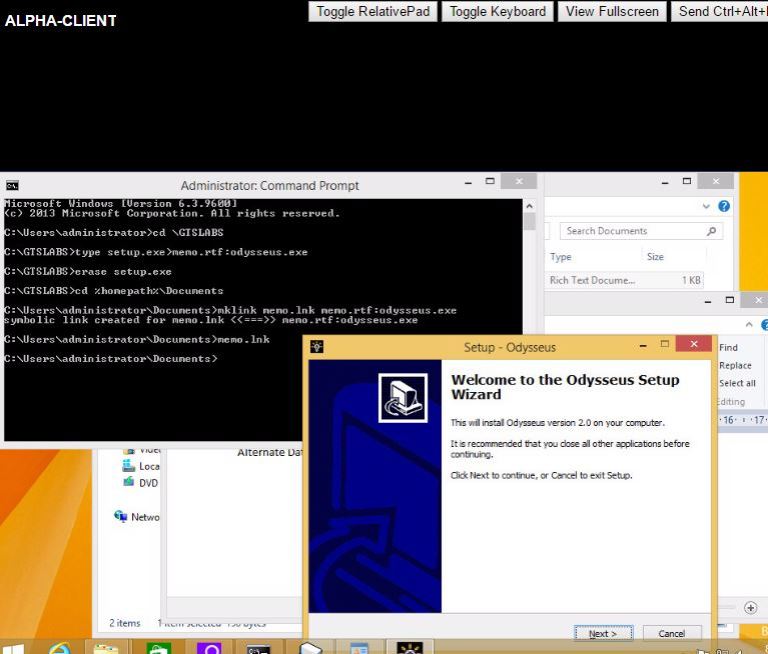
Cancelled the wizard and opened ‘ADS Spy’ instead to scan the system for ‘Alternate Data Streams’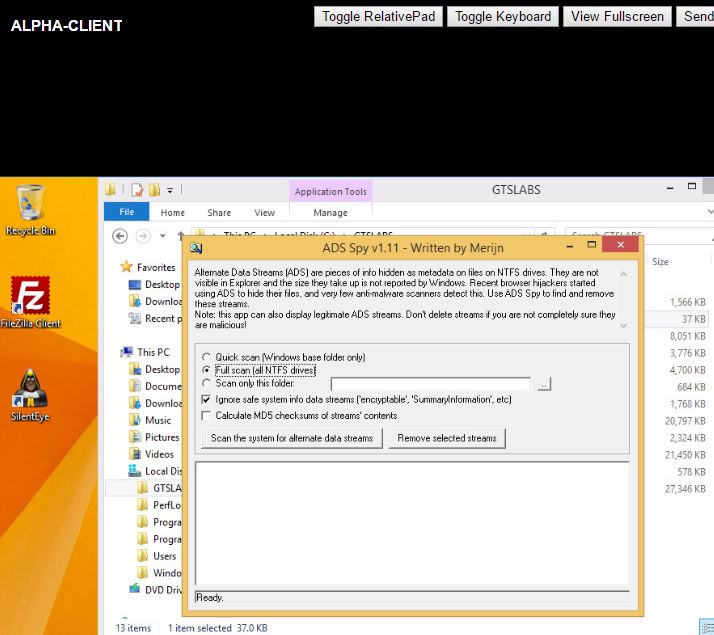
The scan found 3 executable ‘Odysseus’ files in memo.rtf and memo.lnk files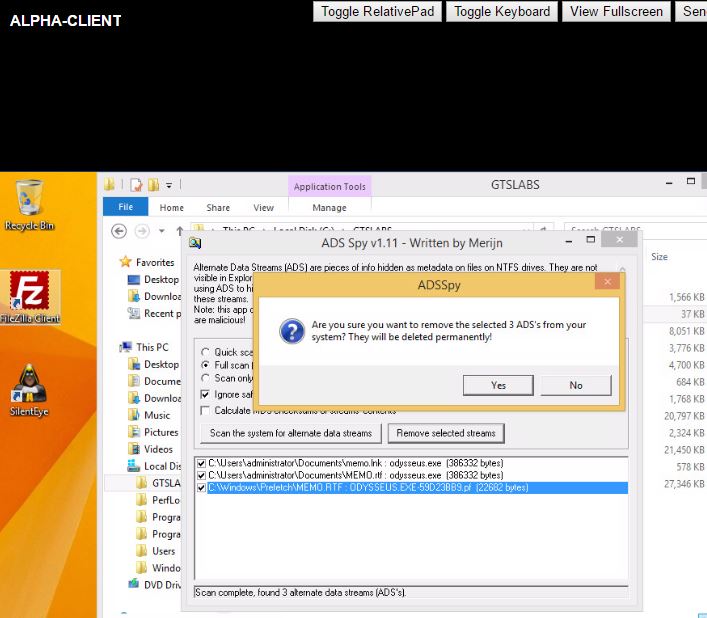 Selected these files and had them removed
Selected these files and had them removed
After deleting these files, tried to run memo.lnk shortcut again, but (as seen below) was told that the file couldn’t been found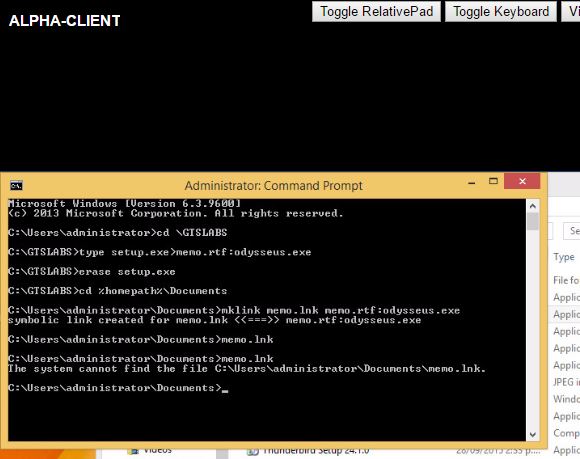
Exercise 4: Completing the Lab
The Client VM was reverted to the ‘pre-lab’ snapshot
